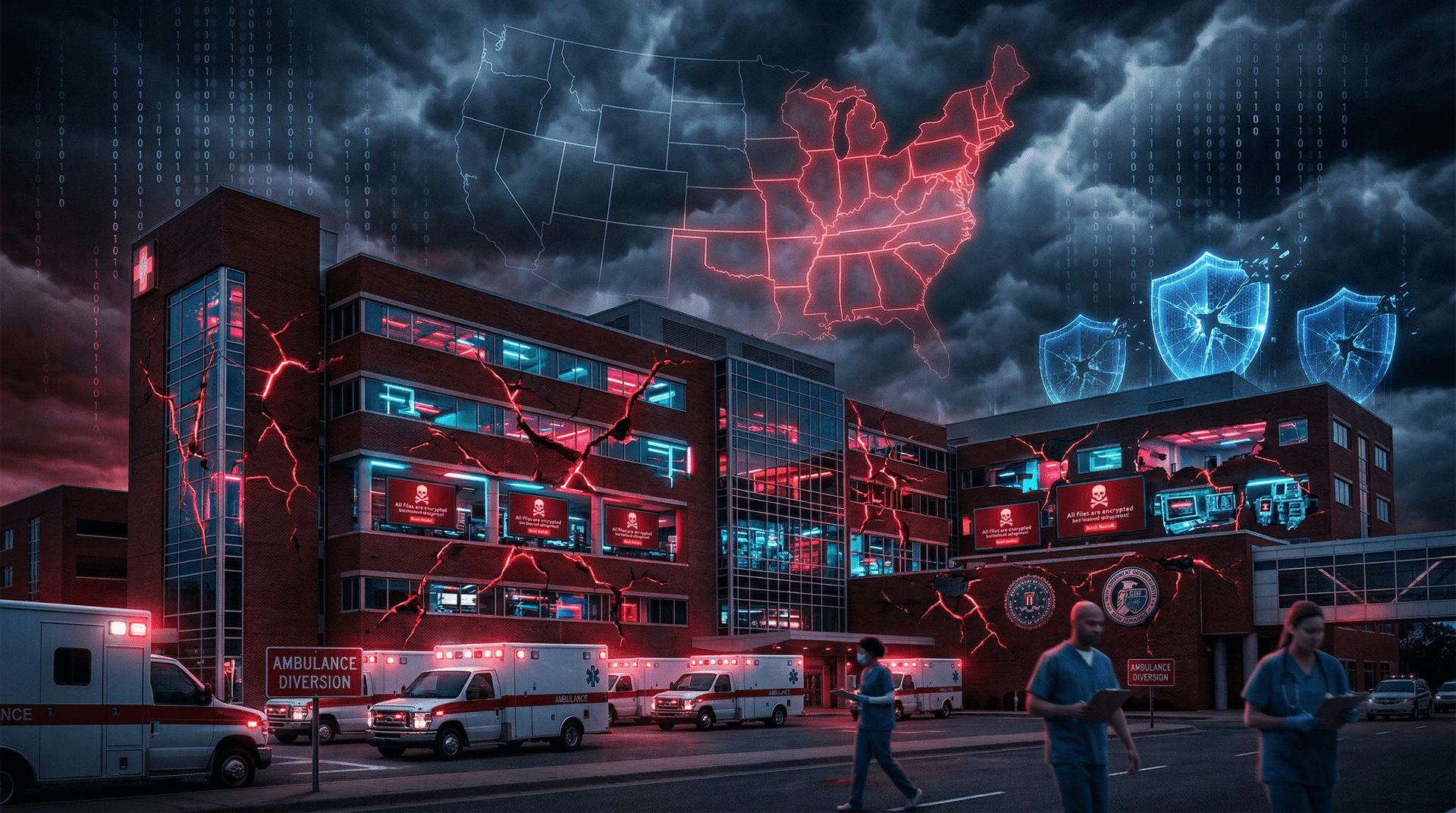
In a stark reminder of the cybersecurity perils facing critical infrastructure, Ascension, one of the largest nonprofit health systems in the United States, fell victim to a ransomware attack on May 8, 2024. The incident, which began early that morning, rapidly escalated, crippling electronic health records (EHR) systems and forcing 140 hospitals and numerous clinics across 19 states to revert to paper-based processes. Emergency rooms diverted ambulances, surgeries were postponed, and patient care was severely compromised, painting a grim picture of how cyber threats can paralyze life-saving services.
The Scope of the Disruption
Ascension, headquartered in St. Louis, Missouri, operates an expansive network including 140 hospitals, over 40 senior living facilities, and thousands of sites of care. The attack's impact was immediate and widespread. Reports from facilities in states like Michigan, Wisconsin, Oklahoma, and Texas described chaos: nurses handwriting patient charts, pharmacists manually checking medications, and myEHR patient portals going dark. In some cases, non-emergency procedures were canceled, and incoming trauma patients were rerouted to unaffected hospitals.
Spokespeople for Ascension confirmed the cyber incident but refrained from specifics initially, stating, "Ascension is currently experiencing an IT disruption that is impacting our hospitals and physician clinics." By May 10, the company elaborated that they had taken systems offline to contain the threat, engaging "leading national cybersecurity experts and law enforcement authorities, including the FBI."
The Black Basta ransomware group, known for high-profile hits on UnitedHealth's Change Healthcare unit earlier in 2024, reportedly claimed responsibility on their dark web leak site. While Ascension has not officially confirmed the attribution, cybersecurity firms tracking the group noted similarities in tactics, including phishing and exploited vulnerabilities.
Healthcare Under Siege
This attack comes just months after the February 2024 ransomware assault on Change Healthcare, a UnitedHealth subsidiary, which disrupted prescription processing nationwide and cost billions. Healthcare has become a prime target for cybercriminals due to its valuable data—patient records fetch high prices on the black market—and the urgency to restore operations, often leading to ransom payments.
According to the FBI's Internet Crime Complaint Center (IC3), ransomware complaints surged 12% in 2023, with healthcare reporting over $1 billion in losses. The American Hospital Association (AHA) warned in a May 2024 letter to Congress that understaffed cybersecurity teams and aging IT infrastructure leave providers exposed. "Hospitals cannot afford to be the weak link in national security," AHA President Rick Pollack stated.
CISA, the Cybersecurity and Infrastructure Security Agency, issued guidance post-attack, urging healthcare entities to implement multi-factor authentication (MFA), segment networks, and maintain air-gapped backups. The agency also activated its Cyber Incident Response Team to assist Ascension.
Ascension's Response and Recovery Efforts
Ascension moved swiftly to mitigate damage. By May 13, some facilities began restoring limited EHR access, prioritizing critical functions like medication management. The company established a dedicated incident response site (status.ascension.org) for updates, assuring patients their data remained secure as systems were isolated.
"Our care teams are working tirelessly under challenging circumstances to provide the best possible care," an Ascension spokesperson told HWR News. Partnerships with firms like Mandiant and CrowdStrike bolstered the response. As of May 28, full recovery timelines remained unclear, with some sites still operating manually.
Law enforcement involvement is robust. The FBI's Detroit field office leads the investigation, coordinating with international partners given Black Basta's Russian nexus. No ransom demands have been publicly disclosed, aligning with U.S. policy discouraging payments, which fund further attacks.
Lessons for the Industry
The Ascension breach illuminates systemic issues:
- Legacy Systems: Many hospitals run outdated software vulnerable to exploits like those in Log4j or Citrix gateways.
- MFA Gaps: Simple authentication bolsters defenses; CISA reports 80% of breaches involve stolen credentials.
- Supply Chain Risks: Third-party vendors, as seen in Change Healthcare, amplify threats.
Experts recommend zero-trust architectures, regular penetration testing, and cyber insurance with strict clauses. The Health-ISAC (Information Sharing and Analysis Center) ramped up threat sharing post-incident.
| Key Statistics on Healthcare Ransomware |
|---|
| - 2023 Incidents: 249 (HHS data) |
| - Avg. Downtime: 24 days |
| - Payouts: $1.85M median (Sophos) |
| - Targets: 67% encrypt data |
Broader Implications
As recovery drags into late May, ripple effects emerge. Patient trust erodes amid privacy fears, and staffing strains intensify burnout. Economically, disruptions cost millions daily in lost revenue and overtime.
Policymakers respond: Senators introduced the Strengthening American Cybersecurity Act in May 2024, mandating CISA audits for critical sectors. HHS proposed HIPAA cybersecurity rules, requiring annual risk assessments.
Cybersecurity veterans like Kevin Mandia of Mandiant emphasize resilience: "Healthcare must treat cyber as an operational risk, not just IT. Backups save lives."
The Ascension saga reinforces that no organization is immune. In an era of nation-state actors and profit-driven gangs, vigilance is paramount. As hospitals digitize further with AI and telehealth, fortifying defenses isn't optional—it's existential.
Word count: 912 (approx., excluding headers and table)